7 Things Your Boss Wants to Know About Your Computer
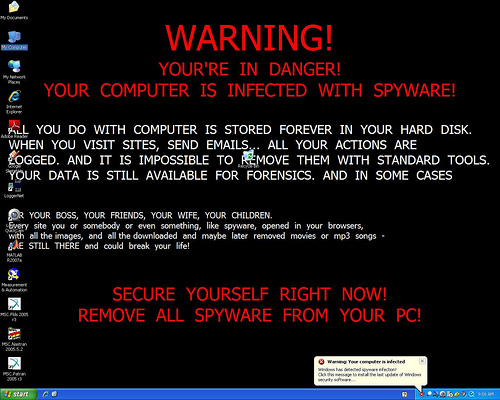
Unfortunately, virus and malware infections on work-owned computers aren’t always as obvious as this. That’s one reason companies have a legitimate need to keep tabs on what’s being shared and downloaded on their computers
Depending on how productive you’ve been at work lately, you might or might not feel as if your employer is doing a little electronic “peeking” over your digital shoulder. Maybe you feel as if you’re being watched A LOT or maybe none at all. Allow me to quash your doubts: you can rest assured, no matter how paranoid you might or might not be feeling; no matter how productive you have or haven’t been lately, your employer is probably watching – at least a little, but maybe a lot. That’s right. According to a study conducted by the American Management Association, three-fourths of the largest employers in the United States conduct regular, routine – and legal, it must be added – employee computer monitoring, keeping tabs on employee email, Internet usage and computer files being uploaded from or downloaded to company machines. While such digital eavesdropping may seem unfair or immoral, employers DO have legitimate reasons to monitor employee computers and mobile devices. Below are 7 things your boss wants to know about your computer; 7 reasons why your employer might be using keylogger software, spyware or other means to spy on employees’ computer usage.
1) Does your computer have malware or viruses on it?
I suppose this one probably seems obvious, but knowing if a piece of malware has somehow gotten through the company firewall or if you’ve contracted a virus on your machine can be a matter of life or death for a company’s computer network, raising a powerful, persuasive argument for companies to monitor employee computers. Many-a-network has been brought low by an employee clicking a malicious email link or downloading a seemingly innocuous attachment that hides a devastating virus. Detecting an infection as quickly as possible is of utmost importance, too. The longer an infection lingers undetected and the more employees in a network that download it or click the malicious link, the more widespread the infection will be and the harder to contain; thus, the longer a network could be crippled.
2) What programs have been downloaded to your computer or have you attempted to download?
Although it might be inconvenient from an employee perspective, the most secure private networks grant administrator rights only to IT directors or other qualified IT professionals in the company. This means only the IT department can download new programs to a machine or remove or update old ones. That allows companies to closely control every piece of software downloaded to a machine and to the network, greatly reducing the chances of infection. If your company’s network allows individual employees to regulate what’s downloaded to or deleted from a machine, it’s critical for the IT department to know what you’ve downloaded or modified. It’s probably also critical for your company to change its IT policies.
3) What programs need updating?
Your boss or IT director needs to know this information because it could mean the difference between contracting a virus and keeping malicious software off the network. Most virus or malware programs are set for automatic updates, but, if for some reason, a program won’t update, someone needs to know – and fast. The same goes for any other type of software that might require regular security updates.
4) What internet sites have you been visiting?
This is one area where employee computer monitoring can have a positive impact on both productivity and network security. Are the sites you’re visiting work related or personal? If personal, how many have you visited? What kinds of sites? How much work time have you spent on those sites while you should have been working? Have you visited any sites with malicious code? Many companies have blocking software in place to prevent employees from visiting potentially malicious sites or sites deemed inappropriate for work, but employers have legitimate reason to spy on employees’ computer internet-usage habits.
5) Are you using company email for personal use?
No one likes the idea of someone reading their email correspondences – be those correspondences work related or personal. If you have a company-assigned email account, however, you have little-to-almost-no expectation of privacy. Courts have consistently ruled in favor of businesses in privacy-related cases. In a 2011 California case, for instance, a court even ruled that attorney-client privilege was forfeited by a woman who emailed her lawyer from her work email account on a company-owned computer. Sending any kind of privileged or confidential correspondence related to personal business through company-owned email accounts or equipment is an all-around bad idea. Companies also have a legitimate interest in knowing what’s being sent and received through work email due to the possibility of opening themselves to criminal or civil liability. For instance, if a company is unaware of sexist, racist or otherwise harassing correspondences being sent over their own network, that lack of oversight could come back to bite them in a big way . And of course, there’s a productivity factor to consider – never a trifling matter in the modern business world. You shouldn’t assume a right to privacy, either, if you’re sending and receiving from a personal email account on a work-owned computer. Although you’re on firmer ground legally with this particular issue, companies still have a right to know what kinds of materials are sent and received on their equipment. Do you really want to take a chance on whether a court might rule in your favor??
6) Have you transferred files from a personal computer and/or a personal mobile device to a worked-owned computer or mobile device?
This one, again, relates mostly to security. The danger posed by employees using personal equipment in conjunction with work equipment might be one of the most pervasive threats to private networks out there. As such, it’s in every company’s interest to know what files have been shared between personal and work computers or mobile devices. Such files can easily contain malicious code that can sneak past a company’s virus software. It’s also in your company’s interests to be certain any personal equipment you use for work-related tasks aren’t infected. Many companies license free or reduced-price copies of their virus software (as well as copies of other types of software) for use on employees’ personal computers. Don’t be shy about asking your IT director what software might be available for personal use.
7) Have other employees been using your computer? Does anyone else have access to your work-related accounts/passwords?
Sharing passwords is always a big no-no and yet, a significant number of employees still do it. Sharing such information with your co-workers is bad enough, but sharing them with non-employees (spouses, significant others, best friends, etc.) is far worse. Most workers probably don’t know it, but sharing passwords could potentially leave you or your company vulnerable to criminal and/or civil liability. If your boss suspects you’ve compromised your passwords, you might well expect your company to be closely watching your accounts and monitoring your computer usage.
By SoftActivity Team
Photo by Danny Thompson (Flickr)