Advancing technology has allowed businesses and enterprises unique advantages. However, with these advantages come additional unknowns and threats to business continuity.
With many of our business relationships and operations existing online, it is no surprise that there is an increased security risk and companies can quickly fall victim to a data breach. And while much of the time a data breach will come from a malicious outsider, companies need to also protect against a trusted insider.
Insider threat detection and prevention is vital to every organization, no matter the size, industry, or location. Consequently, it’s imperative that your security team is able to recognize the signs and indications of security risks so you can defend your network from paralyzing data breaches as well as data theft.
So, we’ve put together this guide to help you understand and defend against insider threats. This guide will go over:
- What an insider threat is
- Warning signs of an insider threat
- Cutting edge technologies that can combat an insider threat
- Preventing an insider threat
- Building an effective insider threat program
- And how SoftActivity’s monitoring software can help with insider threats
What is an Insider Threat?
An insider threat is a cybersecurity risk posed to an organization when a person with authorized access misuses that access to negatively affect the organization’s critical systems or data.
An insider incident could be caused by a malicious external threat, but most of the time, there is no malicious intent with an insider threat incident. Instead, an unintentional insider threat is often due to weak third-party firewalls or negligent employees that could pose a significant security risk.
The insider individual doesn’t necessarily have to be an employee. Partners, third-party vendors, and contractors can also be considered an insider risk.
There are a number of different insider profiles. Among some of the most common insider threat risk parties include:
- Malicious insider or malicious employee
- Negligent insider or negligent employee
- Third-party contractors and vendors
- Business partners
To better prevent an insider incident, your insider threat security plan needs to stay on top of suspicious activity. Suspicious activity can be difficult to spot as malicious insiders will work actively to avoid attention. Negligent insiders can also pose a risk, but you might not be aware that they are a risk until you are aware of their behavior.
Malicious Employees
A malicious insider knows exactly what they are doing when they are stealing information from your company. Often the motive is easy money rather than an attempt to harm their employer.
For instance, an employee might use sensitive information to commit identity theft or fraud for financial gain. Other times, an employee might divulge confidential company information because of philosophical or political motivations.
Negligent Employees
Many insider incidents are caused by careless employees who undermine their organizations by not complying with their business rules and policies, such as clicking on phishing links in emails, inadvertently emailing customer data to external parties, or logging on to the network through unsecured, public Wi-Fi connections.
Unlike the bad actor, the negligent employee unknowingly puts the company at risk of a breach. This category also includes compromised employee devices.
Third-party Contractors and Vendors
Using third-party contractors and vendors opens up your sensitive data to outsiders who do not have a vested interest in your company. This means that these parties pose a potential threat as a malicious insider or accidental insider as they have access to your critical systems.
An accidental insider attack might occur because the third-party has weak security measures and cybercriminals can exploit their systems to infiltrate your network.
Business Partners
Business partners are usually given a similar security level of access to the network and data as employees and contractors. This increases the risk to your organization since the business partners could bypass the security controls you have in place to protect your systems and sensitive information.
Insider Threat Warning Signs

Insider threats can cost you hundreds of thousands of dollars. Additionally, an insider threat can damage your organization’s reputation and hurt the trust you had established with your employees, contractors, and business partners.
Although it’s difficult to spot a potential insider threat, there are some warning signs that can alert you to potential incidents before they occur, such as:
- Risky behavior or a change in normal user behavior
- An employee who leaves a company in poor standing or a former employee who had access to critical assets
- Privileged users accessing large amounts of data
- Unauthorized users gaining access to privileged accounts, servers and/or data
- Attempts to move data offsite
A company can better understand the potential for a data breach by watching insider threat activity. This can be done with consistent surveillance, internet monitoring, and employee monitoring tools. By monitoring normal employee behaviors, normal internet behaviors, and tracking behavior analytics, your team can more easily spot a threat actor.
When you are threat hunting, consider the following:
- Each employee will show a regular pattern of activity. This might fluctuate based on the time of day, the current work environment, or personal stressors. However, in general, you can gauge when an employee or insider is exhibiting normal behaviors, and when they are exhibiting insider threat behavior or anomalous behavior. When user activity fluctuates, then your security team can step in to understand why behavior has become aberrant. You may be looking at a disgruntled employee.
- The more your network is accessed and open, the more risk there is. So consider what security threats can be accessed through a weak or public access point, and only provide privileged user access to a limited number of users.
- Use behavioral analytics in order to track behavioral trends and to add to your threat intelligence portfolio. A security analytics platform and employee monitoring software can contribute to this data.
- You can expect a former employee, past business relationships, and vendors and contractors to be potential insider threats either intentionally or unintentionally. Limit the number of people with access to a privileged account or your company’s critical infrastructure.
- Internet monitoring software can alert you to when an insider is attempting to move data offsite. This includes insiders uploading large files to personal cloud applications, downloading large files to external storage devices, such as USB flash drives, or sending large numbers of emails with attachments outside the company.
- Keep an eye out for insiders – employees or otherwise – who are downloading massive amounts of data. It’s very easy for these malicious insiders to download a few terabytes of data remotely and distribute that data to others quickly.
- Unauthorized insiders will test the waters to determine exactly what systems and data they can access. In this case, warning signs include attempts by users to access servers and data they shouldn’t be accessing and/or requesting access to data that isn’t related to their roles or jobs.
Cutting-edge Technologies to Combat Insider Threats

In the past, enterprises have implemented such technologies as firewalls and proxies to deal with external threats. However, as insider threats increase, cutting-edge technologies are being developed to handle these problems.
Some of these technologies include:
Data loss prevention
Data loss prevention software uses business rules to classify and protect confidential and critical information so that unauthorized users aren’t able to maliciously or accidentally share data that could put your organization at risk.
Machine learning
Machine learning and artificial intelligence (AI) software uses algorithms to detect patterns. Because a user’s malicious actions can be spread across numerous systems and data points, it’s difficult to quickly detect these actions. However, using identifiable algorithms, machine learning combined with user behavior analytics can look for anomalies across data systems to more rapidly detect insider threats.
User behavior analytics (UBA)
User behavior analytics (UBA) technology analyzes the historical data logs of user activity to identify traffic patterns of user behaviors. You can use the data that’s collected to create a baseline of normal behavior. Then when a user’s behavior deviates widely, you can address the threat. Read SoftActivity’s guide on UBA.
Privileged access management
This software helps you prevent authorized users from misusing their privileged access. Privileged access management technology monitors and authorizes privileged users in the key systems across the company. This software is critical in mitigating insider threats.
How to Prevent Insider Threats

To protect your network and your confidential data, it’s imperative that you implement a system to detect insider threats.
Following these nine insider threat prevention tips will help you ensure that your company is safe from malicious employees:
- Train your new employees and contractors on security awareness before allowing them to access your network. Also, incorporate information about unintentional and malicious threat awareness into regular security training for all your workers.
- Watch for the movement of data as it travels within and outside your environment, e.g., as it moves onto devices or into the cloud. Encrypt sensitive corporate data at rest or as it’s traveling over a network using suitable software or hardware technology. That way if a rogue employee or third-party worker steals a hard drive from a server or captures traffic, for instance, that individual will be unable to access your confidential data.
- Address endpoint security by ensuring the physical security of employee devices as well as the corporate data stored on those devices.
- Monitor for shadow IT by looking for tools and apps that haven’t been approved by your IT and security teams because they may compromise your sensitive data.
- Set up third-party employees, including contractors, with temporary accounts that expire on specific dates, such as the end of their projects or contracts. This ensures that these individuals can’t access your systems after they finish their work. If necessary, you can always extend the expiration dates of those accounts.
- After staff members leave your company, be sure to remove their access to your network by disabling accounts as soon as possible. Your human resources staff as well as your employee managers should contact the IT department when employees leave, plan to leave, or are terminated.
- Implement a solid asset management solution that allows you to respond to a lost or stolen device immediately, preventing anyone from accessing the data or the network associated with that device.
- Choose strong security layers to back up your asset management tool with full disk encryption, endpoint anti-virus and anti-malware, as well as a VPN to limit access to a device and the data that’s on it.
- Implement employee monitoring software that helps you reduce the risk of data breaches and the theft of your intellectual property by identifying careless, disgruntled, or malicious insiders. Employee monitoring software enables you to set rules to prevent employees from engaging in risky behaviors, such as emailing sensitive company information. The software also alerts you when employees are violating policies so you can put a stop to their actions. For more details read SoftActivity’s guide on employee monitoring.
How to Build an Effective Insider Threat Program

An insider threat program enables you to anticipate and address any risky behavior or destructive behavior before your systems and data are compromised.
Here are six steps to help you build an insider threat program:
1. Understand your critical assets
Ensure your technical and non-technical teams agree on which assets are the most critical. An asset is deemed critical when your enterprise can’t operate because information or assets are in the hands of your competitors.
For information assets, you should document where they live, where they originate as well as who uses them. For physical assets, document where they’re located, e.g., in the office, in a remote location/third-party location, and the types of data they process.
2. Document and enforce controls and policies
Your employees and others won’t take the policies and controls you have in place seriously if you don’t enforce them. Documenting your controls and policies will make it easier for individuals to follow them.
For instance, document the process to handle reports of phishing/spear-phishing attempts, and designate a chain of command to prevent systems and sensitive data from being compromised. In addition, don’t dilute these policies and controls by not enforcing them consistently. Enforcing them in the same way for everyone will minimize the potential that some employees will think they’re being treated unfairly.
3. Monitor, respond to suspicious and disruptive behavior
Teach your managers how to recognize and report on workplace behavior that’s not appropriate, especially when it comes to handling and processing data as well as violations of your organization’s email and social media usage policies, for instance.
4. Set up a security incident response team
This team will be responsible for preventing, detecting, and dealing with all security incidents, including insider threats. This team should include general IT and information security staff members and as well as members of the C-suite.
Provide the team with policies and procedures to handle each situation. Ensure they have the proper training to keep up with the latest tactics and threats so they can identify insider threats as quickly as possible. The goal of this team is to handle the situation in a way that limits damage to your company and reduces recovery time and costs.
5. Conduct insider threat awareness training periodically
Such training ensures that your employees are aware of the indicators of potential threats. These include erratic or unusual behavior as well as malicious activity, including fraud, sabotage, data exfiltration and espionage as well as unwitting violations of your company’s policies. You should conduct this training within 30 days after an employee is hired and then once a year for all employees.
6. Implement strict account management and password practices
Preventing insider threats means you need to require that individuals use stronger passwords. You also need to implement specific policies and practices to identify users with larger numbers of permissions. Your password policy should include requirements for the length and complexity of users’ passwords as well as your expectations for how/if passwords can be reused or shared.
How SoftActivity’s Monitoring Software Can Help With Insider Threats
SoftActivity Monitor is an employee monitoring solution for insider threat protection that helps organizations:
- Protect against IP theft and inappropriate computer use at work;
- Improve staff productivity;
- Log and store computer usage records for compliance auditing purposes;
- Perform security incident investigations.
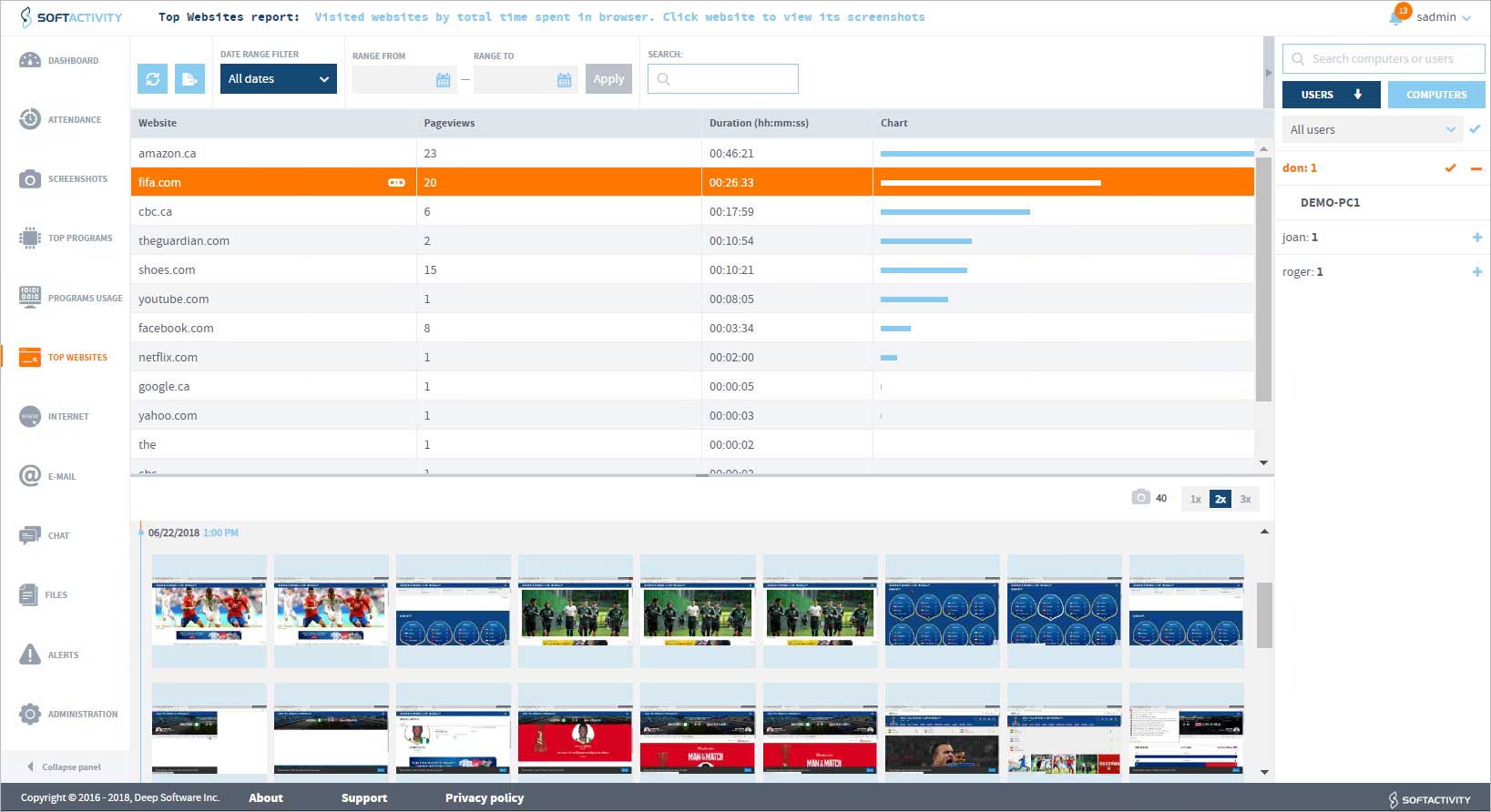
SoftActivity Monitor is very useful in preventing confidential data from leaving the network while letting users focus on their core business. The software is completely invisible to monitored users and only administrators have the capability to install or remove the application.
SoftActivity Monitor enables admins to view any computer within a network in real-time. It is capable of tracking activities such as websites visited, used apps, email, keystrokes logging, among others. The app also lets managers view multiple computers simultaneously, giving them ample time to troubleshoot potential problems even before they occur.
Additionally, you can get reports on how users spend their time at work as well as set up alerts that are triggered when users break your company’s computer/Internet usage policy. With SoftActivity Monitor, you can see disasters coming and prevent them from happening.
Download your SoftActivity Free Trial now!
Conclusion
Insiders pose a dangerous security threat to your data and systems and it can come from a malicious act or an unintentional threat actor.
But rather than accepting the inevitability of an insider attack, you can defend against an insider threat by adopting a more aggressive stance toward insider threat prevention. The key part of this approach is implementing employee monitoring software to help identify careless, disgruntled, or malicious insiders so you can reduce the risk of data breaches and the theft of your intellectual property.
Related:
- 31 Insider Threat Stats You Need To Know In 2021
- 10 Ways to Mitigate Insider Data Loss Prevention Risks
- Do I Really Need To Worry About Insider Threats?
- What Should be Done to Protect Against Insider Threats?
- What are User Behavior Analytics and How Can It Protect Against Insider Threats
- The Financial Cost of an Insider Threat
- Insider Threats in the Remote Workforce