The 5 Best Penetration Testing Tools to Use on Your Network
Penetration testing is one of the best ways to find the flaws in your network’s security and figure out what needs to be patched. It is an essential part of any security-minded company’s process and regular security audits are paramount to keeping sensitive data safe.
Luckily, there are a plethora of tools to help get this important job done. A few tools in particular are especially popular among security professionals to help them penetration test their company’s network.
Metasploit
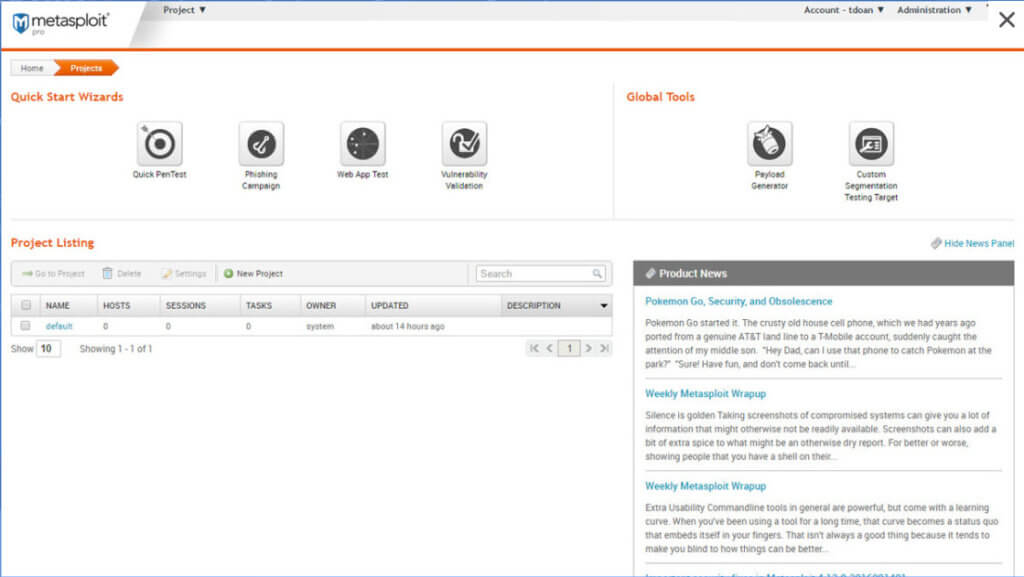
Often touted as “the world’s most used penetration testing framework,” Metasploit has long been considered one of the top must-have tools for both security professionals and the hackers that they try to defend against.
Because of how ubiquitous it is among hackers, it’s a good tool to use for penetration testing because if you can defend against it, then you’ll be able to ward off a lot of hackers from attacking your network with it.
The reason Metasploit is so popular is because it’s basically a “one-stop shop” for penetration testing. It has a massive database of known vulnerabilities and the ways that they can be exploited as well as the tools to execute said exploits. Along with vulnerability scanning and exploitation tools, Metasploit also has anti-forensic and evasion tools, both of which are very important to learn how to defend against.
The only real downside to Metasploit is that it can be rather expensive to purchase the “pro” version, which has the full set of features, but it is more than worth it for any company that is serious about keeping their network secure.
Nmap
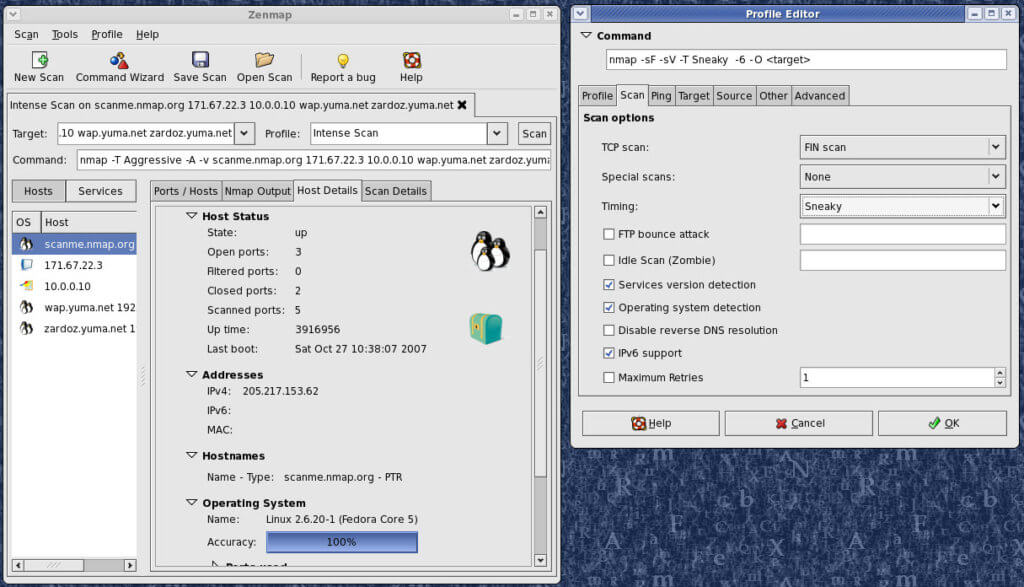
Nmap, which is short for “network mapper,” is an incredibly useful tool for getting the layout of all the devices connected to a network, checking for any open ports, detecting what kinds of firewalls are being used, seeing what hosts are offering what services, and much more. It is pretty much the go-to port scanner for any IT professional.
While it is a pretty common tool for system administrators, it is particularly useful when used for penetration testing.
Because Nmap is capable of discovering services and detecting both the operating systems and software being used on a network, as well as the versions of said software, Nmap is incredibly useful for security auditing. If you can find out what hosts are running outdated software with vulnerabilities, then you can quickly patch them before a hacker tries to exploit them.
Wireshark
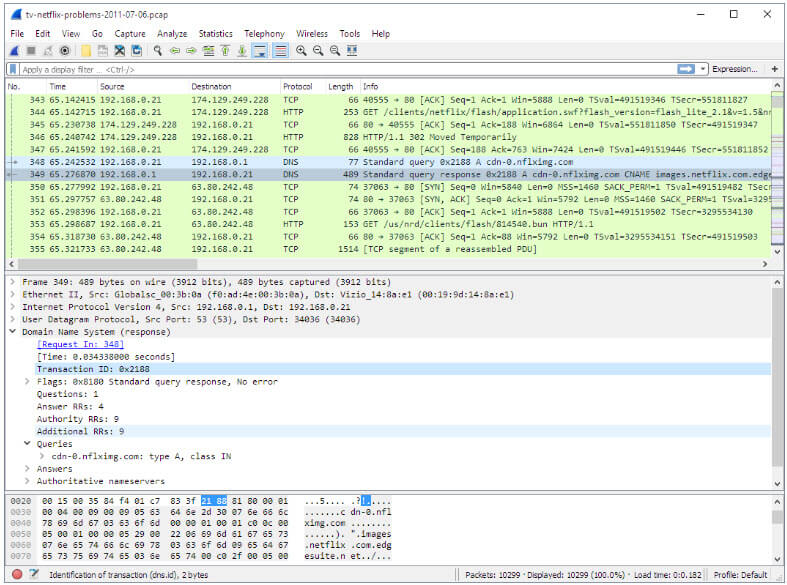
Yet another big name in this list, Wireshark is a network packet analyzer, as well as a common tool in every security professional’s arsenal. In essence, Wireshark allows you to watch the traffic that is being sent over your network and analyze it for any anomalies.
In order to figure out what kind of traffic counts as an anomaly, you’ll first need to get a baseline of the usual traffic on your network. Luckily, Wireshark has some built-in features that allow you to capture everything going through your network to allow you to establish a baseline, and then you can set up filters to only show you traffic that is outside of what is normal for your network.
Not only is Wireshark good to use to monitor your network defensively, but it can also be used to pentest your network.
By letting you examine the kind of data that is going over your network, you can get an in-depth look into what a hacker could see about your network traffic if they managed to gain access to your network. If you notice any sensitive data that is being transmitted over your network unencrypted, then you’ve found a vulnerability and can take steps to fix this issue before anyone gains access to it.
Nessus
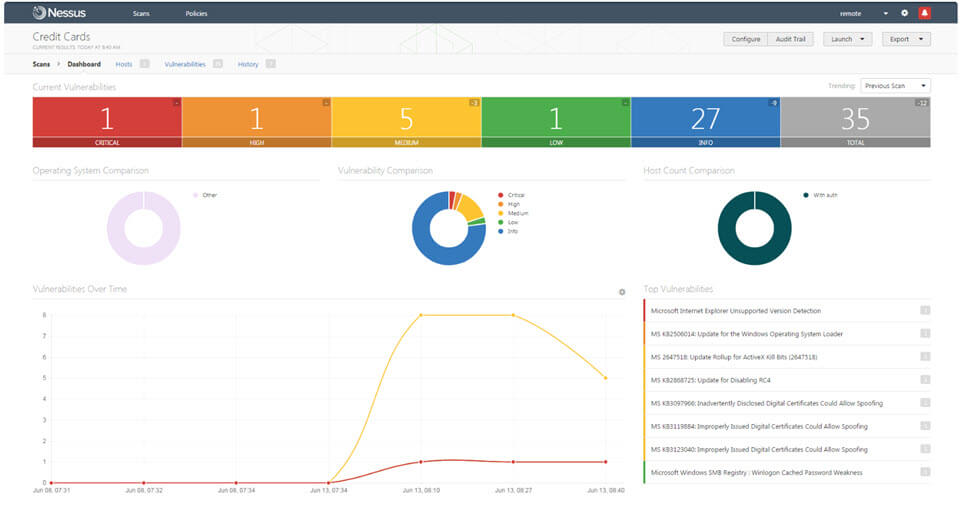
Vulnerability scanners make any security professional’s life significantly easier. Testing for vulnerabilities manually can be a long and tedious process, so automating it speeds things up considerably.
One of the best vulnerability scanners around is Nessus. By using Nessus, you can detect software that is missing patches, check if any system accounts are still using default passwords, scan for open ports and then simulate various exploits on them, and much more.
Nessus is also particularly useful because it has features like letting you schedule security audits, a built-in scripting language that lets you write custom attacks, and the ability to do security tests within a contained environment.
The Exploit Database
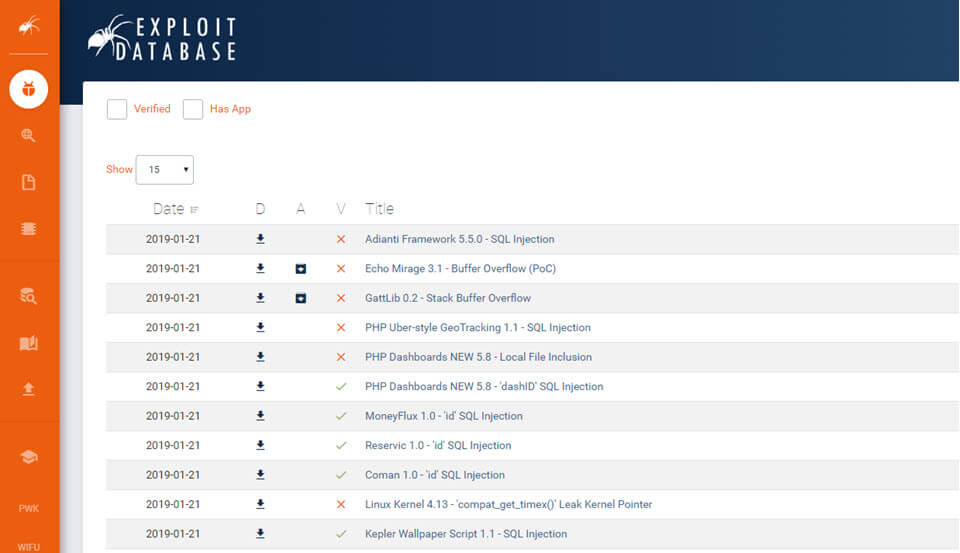
This tool is a little bit different than the others on the list. Instead of being a piece of software that you use directly when pentesting, the Exploit Database (sometimes called “exploitdb” after its Github repo) is a website that contains a plethora of known software vulnerabilities and how to exploit them.
This database is freely available to anyone, so both security professionals and black hat hackers have the same access to this information. That is why it’s a good idea to regularly keep an eye on the database for any exploits involving any software that you use on your network. Because if you don’t learn about it and attempt to fix it, rest assured that somebody out there with nefarious interests already knows about it.
By SoftActivity Team